Nessus Network Vulnerability Scanner
By Stephen Bucaro
Nessus is a proprietary network vulnerability scanning program. Nessus was first
released as free and open source software, but in 2005, its developer closed public
access to the source code and began charging a $1200 annual subscription fee
(a free home version is still available for non-commercial use). Nessus is available
for both Windows and Linux.
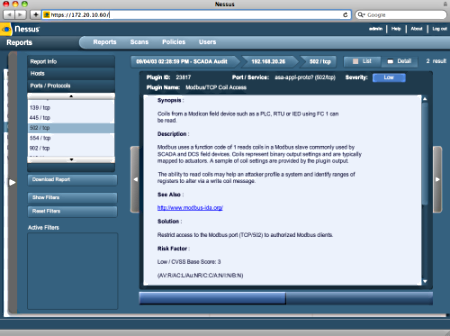
Nessus scans network hosts for vulnerabilities and generates reports on its findings.
It can scan for the following:
• Vulnerabilities that allow a hacker to access a system.
• Misconfigurations that make the system vulnerable.
• Outdated and vulnerable software.
• Insecure, blank, or default passwords.
• Vulnerability to dos attacks.
Starting with version 4, the Nessus moved from standard application format to a
browser based application that utilizes plugins. When Nessus can connect to the
Internet it automatically downloads the latest plugins. Nessus operates as a server
and as a client. The Nessus server performs the actual scanning while the client
presents the user interface and passes commands to the server.
Before you can initiate a scan, you need to make sure the Nessus server is running
on your system. In Task Manager check to see if nessusd.exe is running. If not,
open the Services Management Console, services.msc, scroll to Tenable Nessus,
right-click on the Nessus line and, in the popup menu that appears, choose "Start".
Once the server is running, open your web browser and go to https:⁄⁄[your_IP_address]:8834
or https:⁄⁄localhost:8834 To proceed, you must create a user account in the
Nessus server. When you have logged into the Nessus server, you'll see the Nessus
interface where you can configure scan policies. Scan policies controls the options and
features the scan will use for inspecting target hosts. If you want the scan to login
to the target hosts, you need to provide it with valid credentials to use.
When you start the scan, Nessus will ping the target hosts, probe their ports, attempt
to identify the operating systems, and detect the running services. You can monitor
the entire scan or select a specific host to monitor its particular progress. When the
scan is complete, you can browse through the results on the Nessus client or you can
export the results to a .nessus, .nbe, or HTML format.
More Network Security Articles:
• How to Use the Open Source Intrusion Detection System SNORT
• Understanding the Dangers Your Systems Face
• The Use of HoneyPots and HoneyNets to Trick Hackers
• Wireless Network Security
• How to Secure Your Small Business Network
• Implementing a Secure Password Policy
• Designing Physical Network Security
• How SSL (Secure Sockets Layer) Works
• Network Security Model - Defining an Enterprise Security Strategy
• Data Encryption
| 
